|
--- VERIFICATION OF CONNECTION 2 (Sales data for alpha --> 206.31.65.40 : 1100) ---
Start Time: 1/24/2010 12:15:20 PM for connection 2 (Sales data for alpha -->
206.31.65.40 : 1100)
File: beta\users\bob\budget.xls DIFFERENT ON TARGET
Source Attributes: Timestamp = 1/17/2010 8:21:36 PM Size = 1272 Mask = [0x20]
Target Attributes: Timestamp = 1/17/2010 8:21:36 PM Size = 1272 Mask = [0x20]
Security descriptors are different.
0 BYTES OUT OF SYNC
File: beta\users\bill\timesheet.xls DIFFERENT ON TARGET
Source Attributes: Timestamp = 1/17/2010 8:21:37 PM Size = 1272 Mask = [0x20]
Target Attributes: Timestamp = 1/17/2010 8:21:37 PM Size = 1272 Mask = [0x23]
0 BYTES OUT OF SYNC
File: beta\users\vincent\training.doc DIFFERENT ON TARGET
Source Attributes: Timestamp = 1/12/2010 3:28:20 PM Size = 17 Mask = [0x20]
Target Attributes: Timestamp = 1/20/2010 5:05:26 PM Size = 2 Mask = [0x20]
17 BYTES OUT OF SYNC
Completion Time: 1/24/2010 12:37:44 PM for connection 2 (Sales data for alpha -->
206.31.65.40 : 1100)
Elapsed Time (seconds): 1320.256470
Total Directories Compared: 657
Total Directories Missing: 0
Total Directories Remirrored: 0
Total Files Compared: 120978
Total Files Missing: 0
Total Files Different: 3
Total Files Encrypted: 0
Total Files Remirrored: 1
Total Bytes Skipped: 0
Total Bytes Compared: 18527203678
Total Bytes Missing: 0
Total Bytes Different: 17
Total Bytes Remirrored: 17
Related links and directory attributes have been adjusted.
----- END OF VERIFICATION -----
|
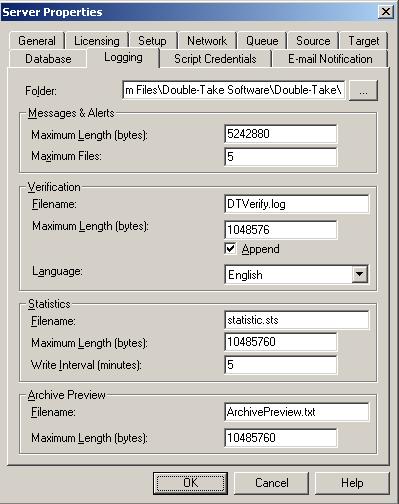
 Sample verification log
Sample verification log Related Topics
Related Topics